
Adventures with VPNs
I recently read an article on the mighty maggot, the Allied Telesis AR2010V VPN router. This article by Jeff Rhys-Jones was pretty interesting and encouraged me to give it a go and put down some observations on the configuration of my VPN router.
Last week we sold a VPN router to a customer who wanted Virtual Private Network (VPN) functionality for six of his remote Window PCs. The AR series routers have a full VPN feature set, so I decided to revisit the lab to try out one of the newer VPN technologies called OpenVPN.
If you don't know what a VPN is—simply put—it makes it possible to connect remote networks as though they’re all together locally at your headquarters. You’re bypassing that dodgy coffee shop hotspot router with the confidence that your browsing and data transfer from your computer and other wireless devices is more secure.
Previously my remote client access VPN technology of choice was the IPSec/L2TP tunnel. I could configure those VPNs in my sleep! It was a great choice because the client was native to recent MS operating systems and it was secure.
However, times change and OpenVPN is more secure and easier to install than IPSec and the OpenVPN server is built-in to my router. Allied Telesis has a lot of firewalls and routers for different applications, including the AR family’s AR3050S and AR4050S, and each of them supports OpenVPN.
There are many ways to implement VPNs. You can find open source software and it's not difficult to create your own OpenVPN server on a Linux platform. But to do this, you’ll need:
- a hardware platform...$$
- someone with the skills to put the software together...$$$
- someone who is familiar with virtualization software..$$
As you can see, this server may actually cost a lot of money and time, along with long-term support and management to assemble and maintain, compared to the purchase of a dedicated VPN router that is fully supported and guaranteed to work properly.
On the other hand, it’s easy to learn the Allied Telesis OpenVPN technology, and I really like it. The PC client was absolutely free, secure and fast to install. Unlike some competitors’ routers, with my trusty Allied Telesis router there is no licensing for up to 100 VPN users making the whole solution truly inexpensive.
The PC client was downloaded from openvpn.net. There are clients for MAC, PC, Android and iPad/iPhone there too.
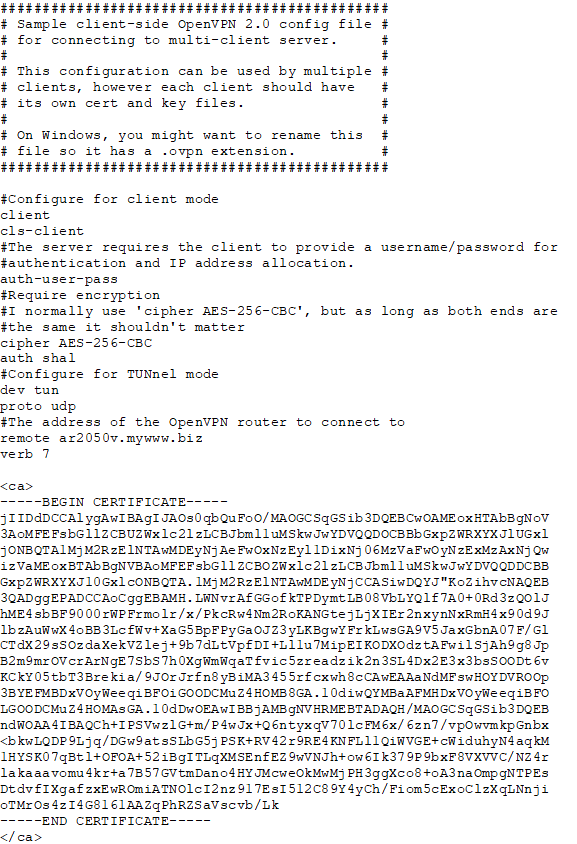
I found the benefit of this PC client is that your integrator/technician can select "edit config" as shown below, then cut and paste the configuration into the client. For the techies out there, you may observe that this configuration file below looks deceptively like a .ovpn file. More information on the .ovpn file can be seen on the Allied Telesis feature guide on OpenVPN.
I used an Allied Telesis AR2050V VPN router to test my OpenVPN server and configured each of these built-in features:
- A RADIUS server, which is used for user authentication
- A dynamic DNS client
- A firewall and NAT, which makes the solution ideal for small- to medium-sized customers
- VPN interfaces
There was no need for an external RADIUS server or even to purchase fixed IP addresses, which really helps to keep costs down.
If you’re a technician and have an Allied Telesis firewall or router, I am more than happy to send my router’s configuration, and give you a couple of hints that will speed installation time down to a few minutes. Feel free to email me here: David_Hornstein@alliedtelesis.com.
Related



