Controlling Devices with OpenFlow
OpenFlow Basic Configuration Example
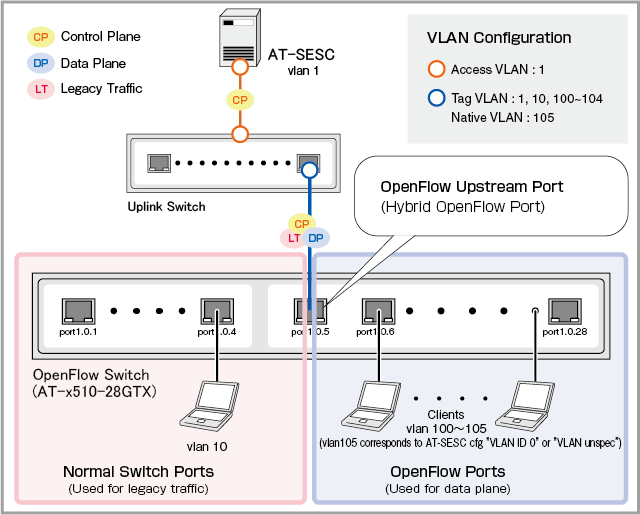
In this section, this is a basic setting example of OpenFlow.For each device connected to the OpenFlow Switch, AT-SESC performs authentication and assigns an appropriate VLAN.
If AT-SESC is configured to work with external applications, AT-SESC also performs the action defined on the System Settings > Trap Monitor Settings page when it's notified of a suspected node by the application.
Those elements are collectively referred to as security policies. Here is a list of elements of security policies:
NoteTo use this function, the feature license is required on the AMF master side. AMF Cloud and SwitchBlade come with the feature license as standard, and other AMF Master devices require an optional AMF Application Proxy license. Please check our website for details.
◼ Configuration
As an example, configure the following network:
| Item Name | Value |
|---|---|
| IP Address | 192.168.1.10 |
| OpenFlow TCP Port | 6653 |
| OpenFlow Switch's upstream port | port1.0.5 |
◼ Device Authentication Data to register on AT-SESC
| Item Name | Value |
|---|---|
| Device1 | |
| Device ID | Device1 |
| MAC Address | 00:00:00:00:00:01 |
| VLAN to assign | VLAN100 |
| Device2 | |
| Device ID | Device2 |
| MAC Address | 00:00:00:00:00:02 |
| VLAN to assign | VLAN101 |
| Device3 | |
| Device ID | Device3 |
| MAC Address | 00:00:00:00:00:03 |
| VLAN to assign | None |
Configuring OpenFlow Switch
The case of using AT-x510-28GTX is explained as an example.Refer to the AlliedWare Plus Product's command reference manual for the commands described below.
- Disable the VCS feature because it's not supported to use OpenFlow on stacked devices.
awplus(config)# no stack 1 enable ↓
Note
Make sure to save the configuration and reboot the switch after disabling the VCS feature.
- Create VLANs for packet forwarding on OpenFlow ports.
awplus(config)# vlan database ↓
awplus(config-vlan)# vlan 100-104 ↓
- Create a VLAN for packet forwarding on ordinary switch ports.
awplus(config-vlan)# vlan 10 ↓
- Create a VLAN and configure it as the OpenFlow control VLAN.
awplus(config-vlan)# vlan 4090 ↓
awplus(config)# openflow native vlan 4090 ↓
- Assign an IP address to a VLAN to communicate with the controller (control plane).
awplus(config)# interface vlan1 ↓
awplus(config-if)# ip address 192.168.1.1/24 ↓
- Specify an IP address and TCP port of the OpenFlow controller (AT-SESC).
awplus(config)# openflow controller oc1 tcp 192.168.1.10 6653 ↓
- Assign the VLAN to ordinary switch ports.
awplus(config)# interface port1.0.1-1.0.4 ↓
awplus(config-if)# switchport access vlan 10 ↓
- Configure port 1.0.5 to 1.0.28 as OpenFlow ports.
Disable the MAC address thrashing protection which cannot be used on OpenFlow ports.
awplus(config)# interface port1.0.5-1.0.28 ↓
awplus(config-if)# openflow ↓
awplus(config-if)# thrash-limiting action none ↓
- Add the following configurations to prevent control packets from being sent out on the OpenFlow ports.
Table 3: Sample Configuration Data
Item Name Value System-wide configuration Disable RSTP and MLD Snooping On the VLANs for packet forwarding on OpenFlow ports Disable MLD Snooping On the OpenFlow control VLAN Disable IGMP Snooping TCN Query Solicitation and MLD Snooping.
awplus(config)# no spanning-tree rstp enable ↓
awplus(config)# no ipv6 mld snooping ↓
↓
awplus(config)# interface vlan100-104 ↓
awplus(config-if)# no ipv6 mld snooping ↓
↓
awplus(config)# interface vlan4090 ↓
awplus(config-if)# no ip igmp snooping tcn query solicit ↓
awplus(config-if)# no ipv6 mld snooping ↓
Note
If the LDF is globally enabled on the switch, make sure to disable the LDF on all the OpenFlow ports.
- Configure the upstream port 1.0.5 as a tagged port and assign the control plane VLAN and the ordinary port VLAN to the port.
Also disable the ingress filtering to be able to receive any other tagged VLANs.
awplus(config)# interface port1.0.5 ↓
awplus(config-if)# switchport mode trunk ingress-filter disable ↓
awplus(config-if)# switchport trunk allowed vlan add 1,10 ↓
awplus# write memory ↓
awplus# reboot ↓
reboot system? (y/n): y ↓
Configuring AT-SESC
- Registering Network
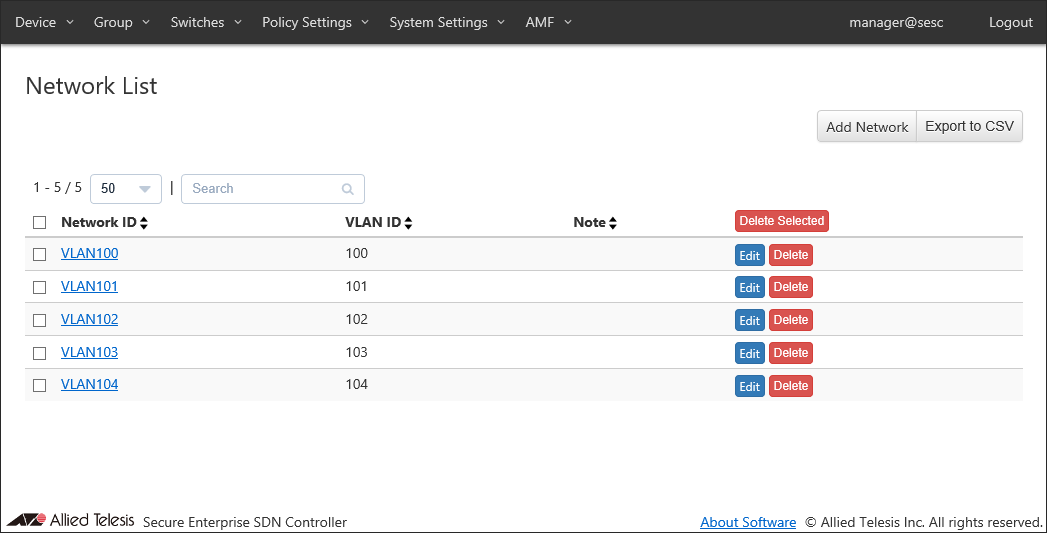
Open Add Network page from the Policy Settings > Network List page to register a network to which devices is assigned.
Enter a Network ID and a VLAN ID, then click "Submit".
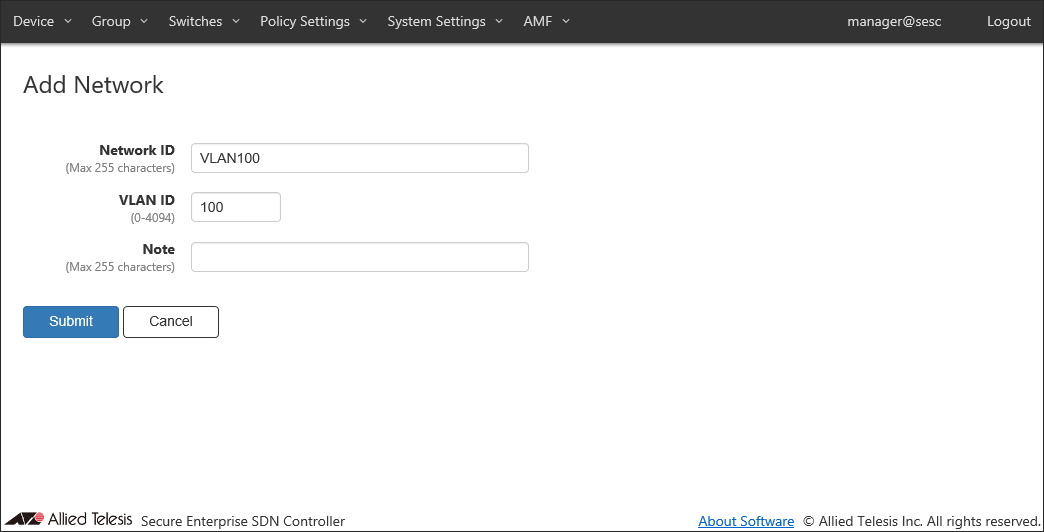
You can view the added network on the Policy Settings > Network List page. Repeat this process until you add all required networks.
- Registering Device
Open Add Device page from the Device > Device List page to register devices.
Enter a device ID, then click the "Add Interface" button to open the "Edit Interface" dialog.
Enter the device's MAC address and click "Submit".
Those elements are collectively referred to as security policies. Here is a list of elements of security policies:
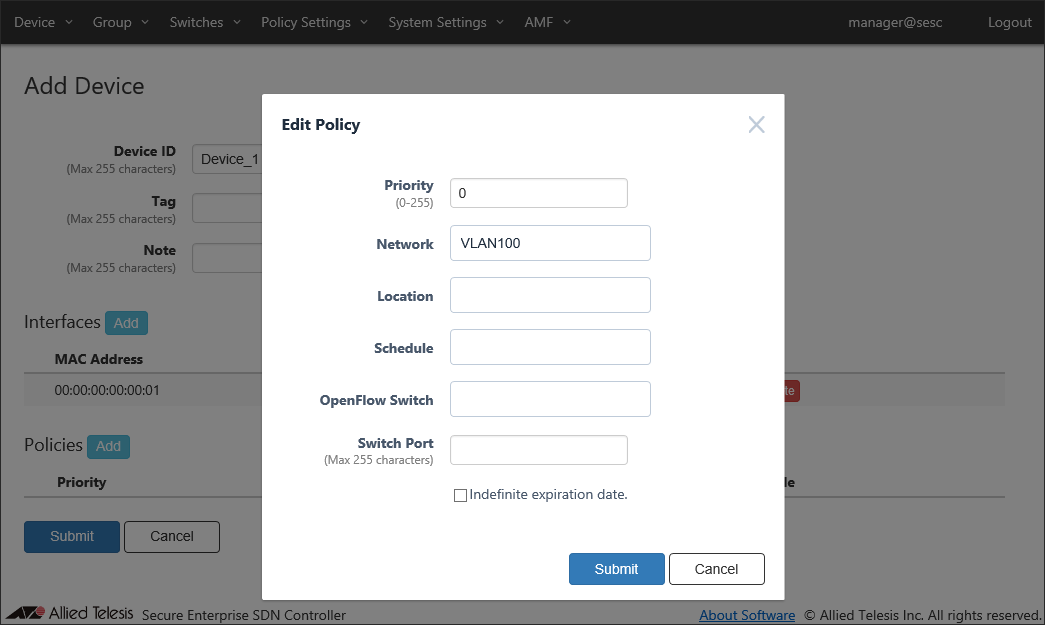
Click "Add" in "Policies" section to specify a network to assign to the device.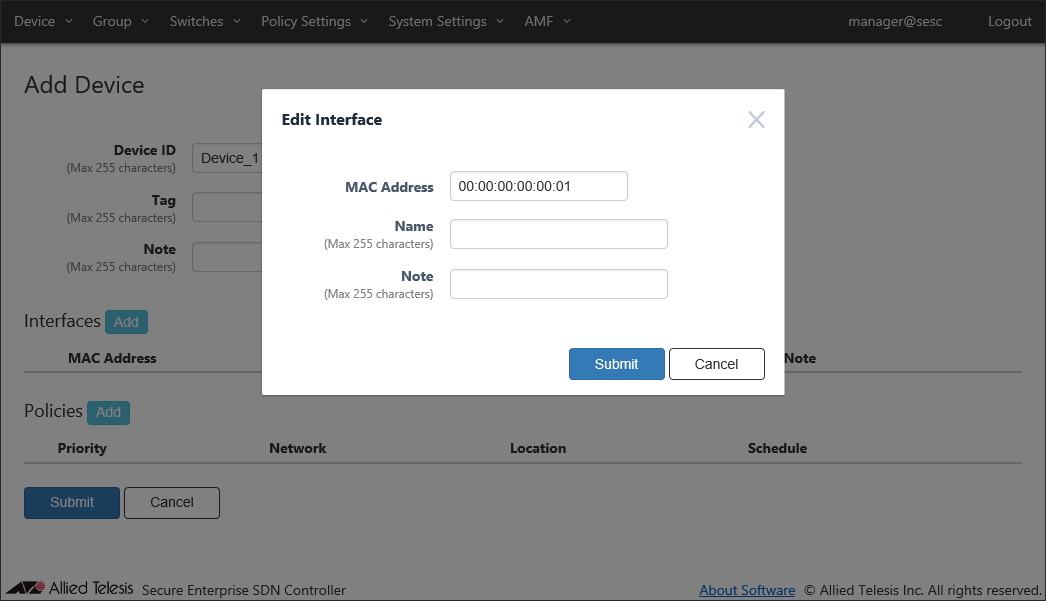
Enter a priority, select a network to assign and click "Submit".
Once the interface and the policy are added, click "Submit" to register the device.
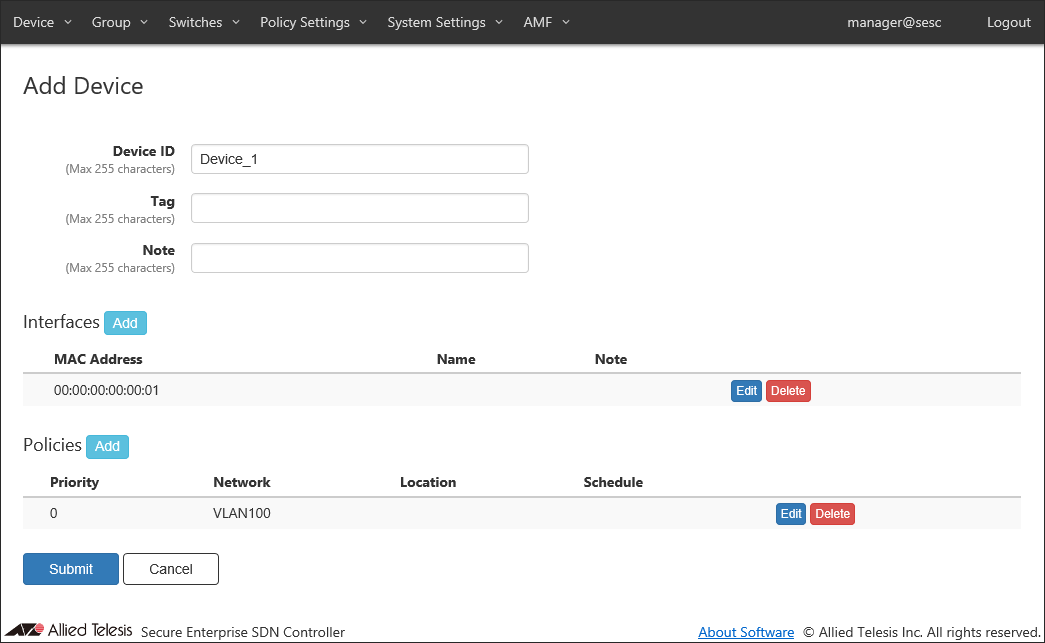
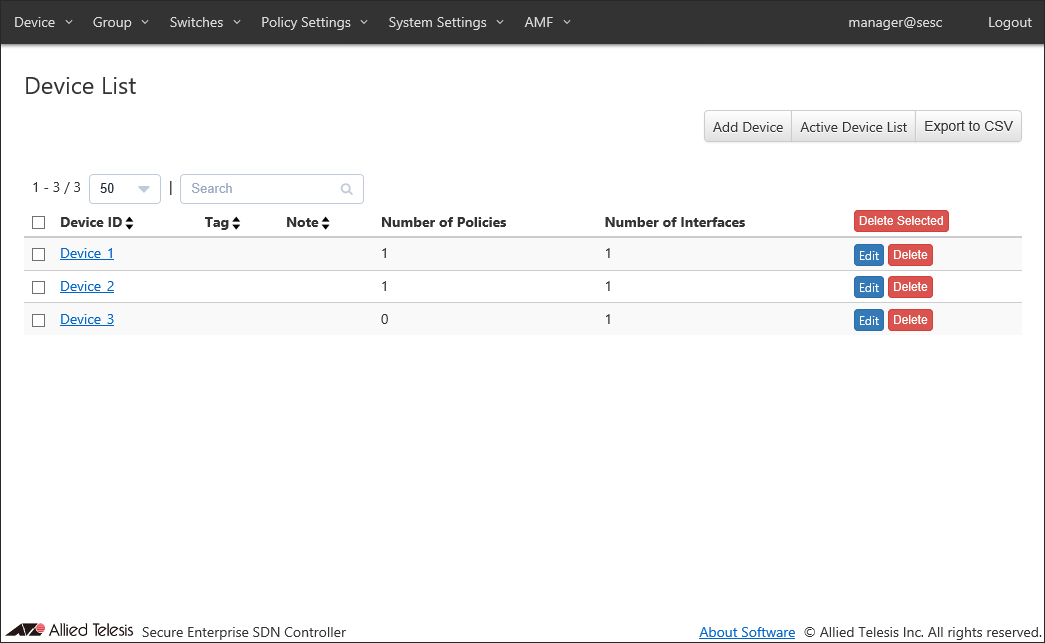
You can view the added device on the Device > Device List page. Repeat this process until you add all devices.
- Registering OpenFlow Switch
Connect the AT-SESC and the OpenFlow Switch to the network.
Once the connection between AT-SESC and the OpenFlow Switch is established, connected OpenFlow Switches are displayed on the Switches > Active OpenFlow Switch List page.
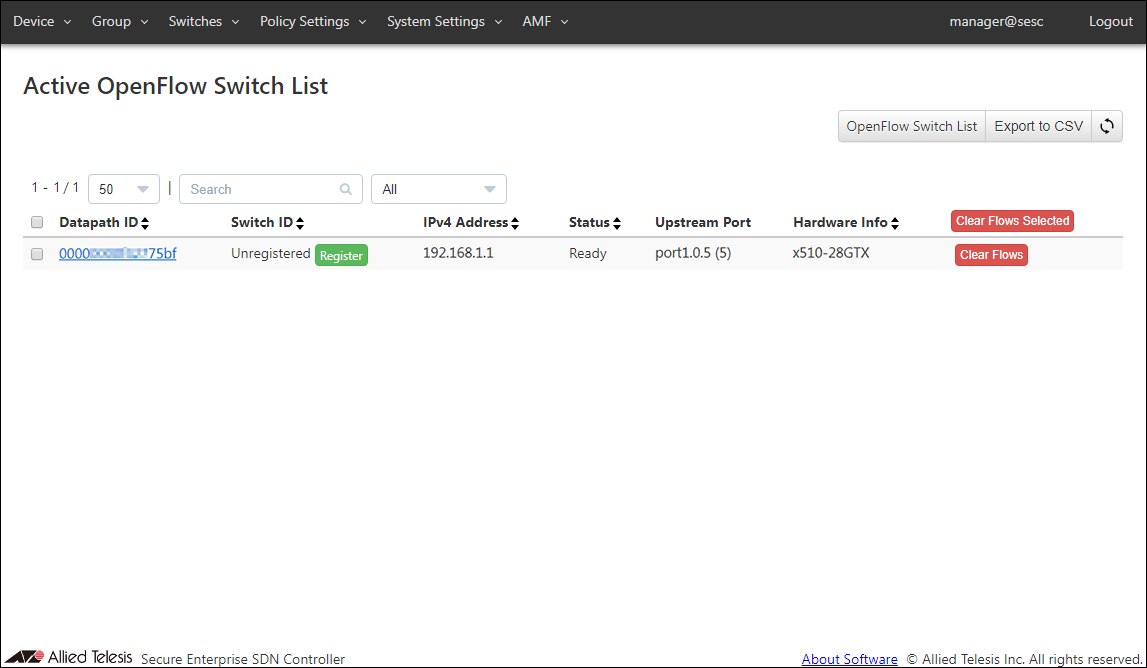
Click "Register" in "Switch ID" column to open the Switches > Add OpenFlow Switch page.
If the default name looks good, just click "Submit".
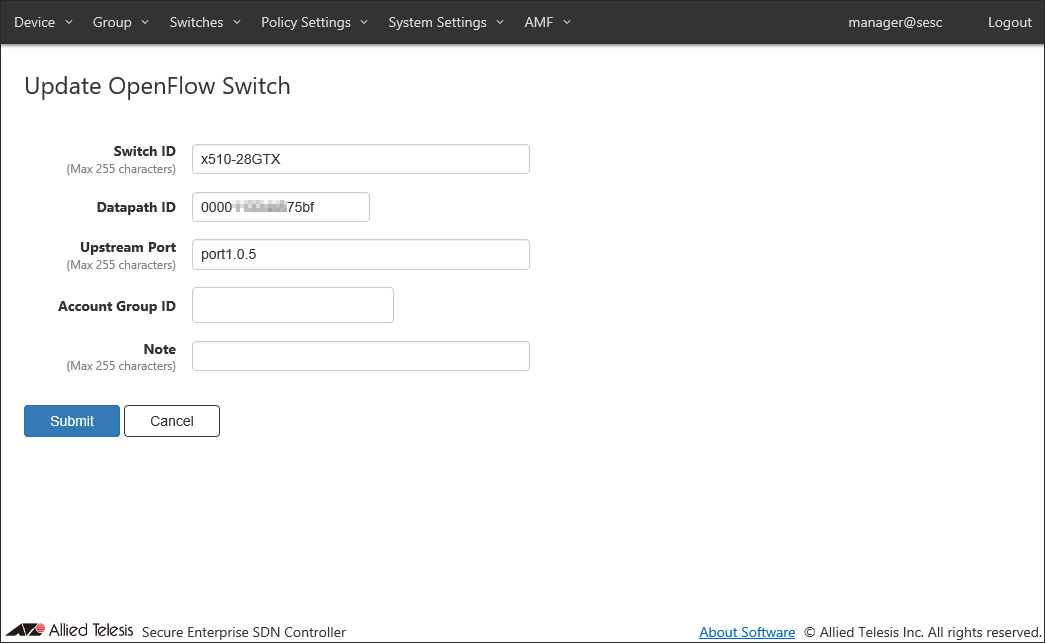
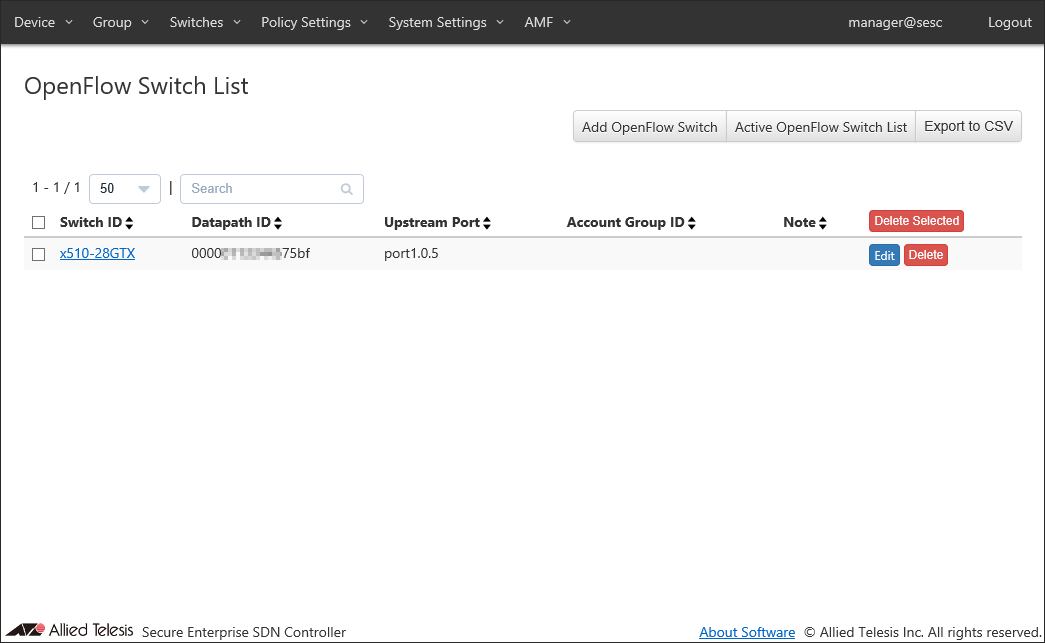
You can view the added OpenFlow Switch on the Switches > OpenFlow Switch List page.
Note
If you are not using location-based authentication or OpenFlow Switch authentication, you do not have to register OpenFlow Switches.
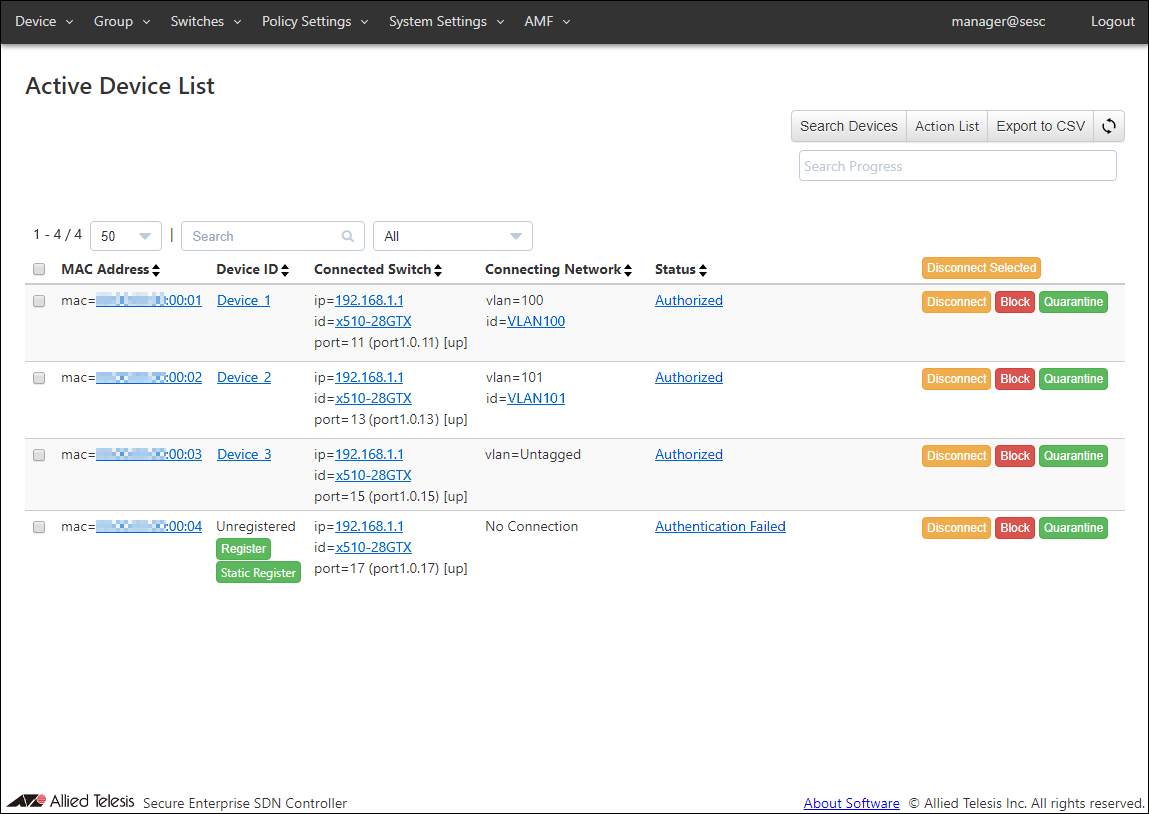
AT-SESC authenticates devices connected to the OpenFlow Switch using the registered authentication data.
You can view the authentication results on the Device > Active Device List page.
Those elements are collectively referred to as security policies. Here is a list of elements of security policies:
OpenFlow Switch Configuration (AT-x510-28GTX)
! no stack 1 enable ! no spanning-tree rstp enable ! no ipv6 mld snooping ! vlan database vlan 10 vlan 100-104 vlan 4090 ! openflow controller oc1 tcp 192.168.1.10 6653 openflow native vlan 4090 ! interface port1.0.1-1.0.4 switchport access vlan 10 ! interface port1.0.5-1.0.28 openflow thrash-limiting action none ! interface vlan1 ip address 192.168.1.1/24 ! interface vlan100-104 no ipv6 mld snooping ! interface vlan4090 no ip igmp snooping tcn query solicit no ipv6 mld snooping ! |
14 Jun 2021 09:30